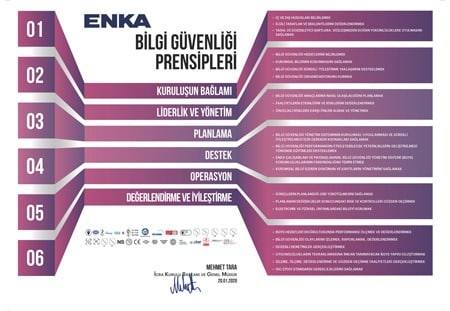
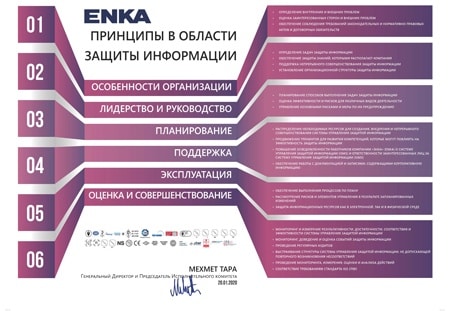
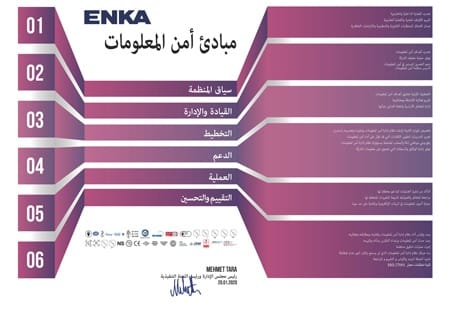
The Information Security Management System (ISMS) was established to protect the confidentiality, integrity and accessibility of information within ENKA by applying asset and risk management processes and to assure the interested parties of managing the risks properly. ISMS is a part of ENKA’s corporate processes and general management structure. Information security processes were taken into consideration in the design and controls of information systems and scaled in accordance with ENKA’s needs.
ENKA has implemented a comprehensive Information Security Management System (ISMS) based on the ISO/IEC 27001 ISMS standard to achieve its information security objectives.
The processes, information and employees pertaining to the activities carried out in the headquarters of ENKA İnşaat ve Sanayi A.Ş. within the scope of; design and engineering, procurement and supply chain management, occupational health – safety and environmental management, quality management, machinery and equipment management, sustainability & compliance, corporate communication, human resources and administration, information technologies, finance, accounting operations, financial control, insurance and risk, investor relations, legal affairs, management and execution of oil, gas & petrochemical and power plant projects, operate an Information Security Management System in accordance with ISO/IEC 27001 information security management system (ISMS) standard.
ENKA complies and was certified with ISO/IEC 27001 standards in the year 2020.